Wallet Hygiene for MEV Traders: A 2026 Self-Custody Playbook
**Answer first** — A MEV trader needs at least three wallet tiers: a *hot strategy wallet* (small float, signs every tx, lives on your VPS), a *warm treasury wallet* (bulk capital,
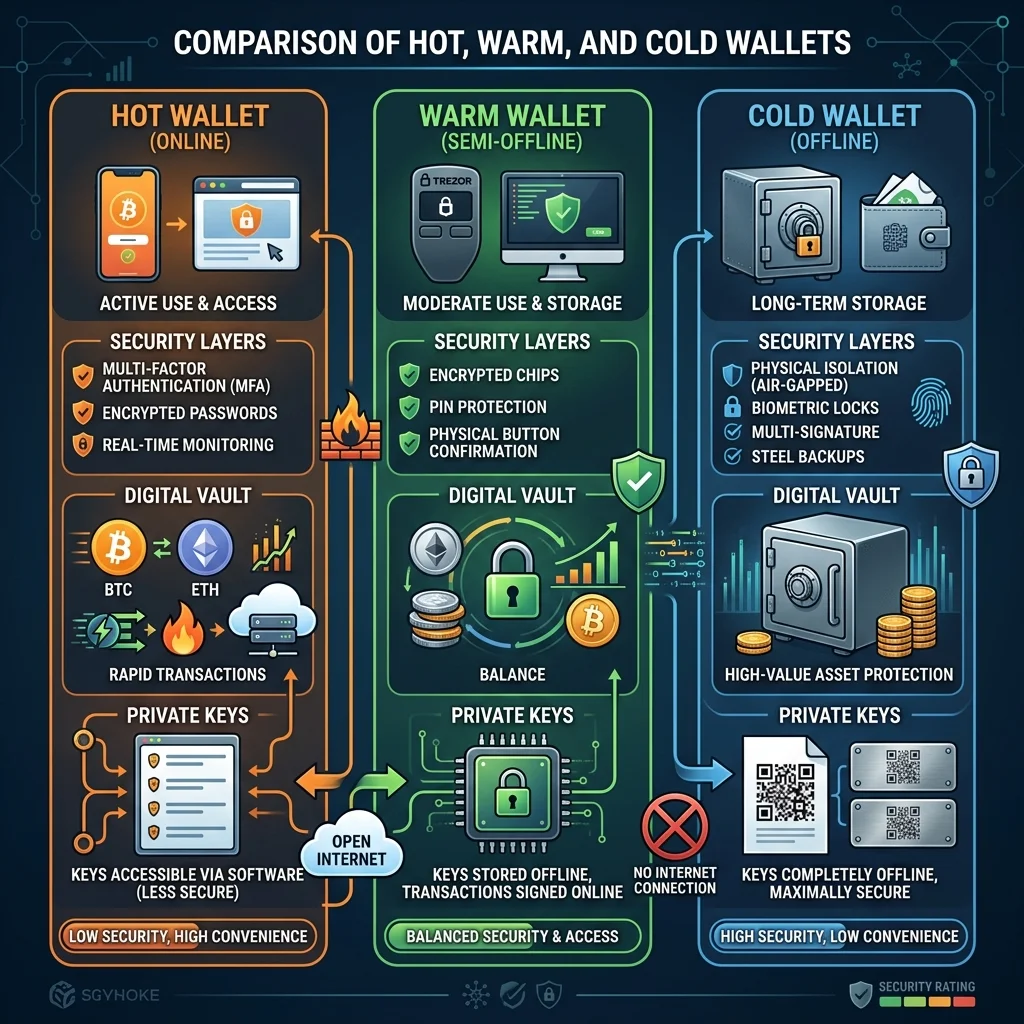
Answer first — A MEV trader needs at least three wallet tiers: a hot strategy wallet (small float, signs every tx, lives on your VPS), a warm treasury wallet (bulk capital, hardware-secured, signs only sweeps and top-ups), and a cold reserve (long-term holdings, never signs anything operational). Anyone running everything from a single hot wallet is one VPS compromise away from total loss. The setup takes 30 minutes; the alternative is paying for that 30 minutes in five-figure increments.
If you haven't read Crypto Trading Bot Security Best Practices, do that first. This article is the wallet-specific deep-dive.
Why Single-Wallet Operations Fail
A typical compromise scenario:
- Operator runs FRB Agent on a VPS.
- The bot signs every fill from the same wallet that holds all bankroll.
- VPS is compromised — through a stolen SSH key, a poisoned dependency, or a malicious package update.
- Attacker reads the wallet's private key from the bot's config.
- Entire bankroll drained in one block.
Step 4 is the failure point that wallet hygiene prevents. The hot wallet should never have material capital exposure.
The Three-Tier Architecture
┌─────────────────────┐
│ Cold Reserve │ Hardware-only, never online
│ (>50% of stack) │ Multisig, ideally
└─────────┬───────────┘
│ Manual transfer (rare)
▼
┌─────────────────────┐
│ Warm Treasury │ Hardware-secured, signs sweeps + top-ups
│ (35–45% of stack) │ Online but inactive between operations
└─────────┬───────────┘
│ Top-up: weekly
│ Sweep: weekly
▼
┌─────────────────────┐
│ Hot Strategy │ On VPS, signs every fill
│ (5–15% of stack) │ Limited to ~1 week of working capital
└─────────────────────┘
The proportions are tunable. The separation is not.
Hot Strategy Wallet Rules
The wallet your bot signs from. Configure for blast-radius minimization:
- Never funded above 1 week of working capital. Compromise loses one week, not one bankroll.
- No token approvals to unfamiliar contracts. Use approval revoker tools weekly.
- Per-strategy isolation if practical. Liquidation and arb wallets separated means a bug in one doesn't drain the other.
- Unique keypair generated specifically for the VPS. Never reuse a key from another machine.
- Backup: yes, but encrypted and offline. A photographed seed phrase isn't a backup.
Warm Treasury Wallet Rules
The middle tier — bulk capital, but online and ready to top up the hot wallet.
- Hardware wallet (Ledger, Trezor, GridPlus). Mnemonic never typed into software.
- Distinct seed phrase from cold reserve. A compromise of warm shouldn't expose cold.
- Signing requires physical confirmation. No "sign anything" sessions.
- Connected only during operations. Disconnect between top-ups.
- Whitelisted destinations. Top-ups only go to your own hot wallet address.
Cold Reserve Rules
Long-term capital. Treat it as if it's unspendable.
- Multisig where practical. 2-of-3 or 3-of-5 with geographic distribution of signers.
- No online exposure. Air-gapped signing for any movement.
- Documented recovery path. Where are the seeds? Who knows? What happens if you're incapacitated?
- Periodic recovery drill. At least annually, prove you can spend from cold without exposing seeds.
- No DeFi exposure. Cold reserve is in native asset (ETH, BTC, SOL, stablecoins), not LP positions.
Key Storage: What Actually Works
Avoid:
- Plaintext keys in JSON files on the VPS
.envfiles committed to any repo- Browser extensions on the same machine as the bot
- Cloud-synced password managers as the only copy
Use:
- OS-level keystore (macOS Keychain, Windows DPAPI) for hot keys
- Hardware wallets for warm
- Air-gapped signing for cold
- Encrypted backup on a hardware-encrypted USB stored in a separate physical location
FRB Agent stores hot wallet keys via the OS keystore by default — see Security for the implementation.
Approval Hygiene
Token approvals are how 80% of "I was hacked" incidents happen. The pattern:
- You approve a router contract for unlimited spend.
- The router has a vulnerability or is replaced via proxy upgrade.
- Attacker drains your wallet using the standing approval.
Mitigations:
- Use bounded approvals (
amount = 2 × expected_trade_size), notMAX_UINT. - Revoke approvals weekly via Revoke.cash or similar.
- Never approve to unverified contracts.
- Audit approval list per wallet monthly.
Wallet Rotation
Rotate hot wallet keys quarterly:
- Generate new keypair.
- Update FRB Agent config.
- Sweep old wallet to warm treasury.
- Burn the old key (delete from all backups).
- Resume operations on new wallet.
A rotated wallet that gets compromised exposes zero capital. A 12-month-old hot wallet exposes 12 months of accumulated approvals and any forgotten capital.
VPS Security (The Non-Wallet Half)
Wallet hygiene only works if the VPS itself isn't trivially compromised:
- SSH key auth only. No password login.
- Firewall to only required outbound ports. Block lateral movement.
- Automated security updates.
- No other workloads on the same VPS. Especially not browser-based ones.
- Monitoring: alert on any process spawning that isn't FRB Agent.
- Snapshot before deploy. Roll back instantly on anomaly.
For full setup see VPS Setup for Crypto Bots.
Multisig for Treasury (Recommended at $50k+)
Above $50k, multisig the warm treasury:
- Safe (formerly Gnosis Safe) is the standard
- 2-of-3 with: yourself, a hardware wallet, and a recovery key held by a trusted third party
- Or 3-of-5 with geographic distribution if you want max resilience
Cost: ~$5–20 per multisig tx. Worth it.
What Happens When Things Go Wrong
If you suspect compromise:
- Pause the bot immediately. Don't try to "trade through" suspicion.
- Move warm and cold capital to fresh wallets. Use hardware-only signing.
- Investigate the VPS. Check for unexpected processes, modified binaries, new SSH keys.
- Rotate every key the VPS could access.
- Forensics: pull logs to a separate machine for review.
Speed matters. The first 30 minutes after detection determine whether warm capital survives.
Recovery Drills
You should be able to:
- Recover hot wallet in 10 minutes (low stakes, easy)
- Recover warm wallet in 1 hour with hardware (moderate)
- Recover cold reserve in 4–24 hours (high friction by design)
If you've never tested, you don't actually know. Run a recovery drill quarterly with $1 in each wallet to verify the path.
FAQ
Do I need a hardware wallet for hot strategy capital?
No — hot wallets need to sign automatically, which doesn't work with hardware wallets. Hot wallet keys live in OS keystore. Hardware is for warm and cold.
Can FRB Agent sign with a hardware wallet?
Not for active strategy execution (latency makes it impractical). Only for periodic top-ups, which can be initiated from the dashboard with a hardware-attached wallet.
Is multisig necessary for everyone?
Below $50k bankroll, the operational complexity of multisig outweighs the security benefit for most users. Above $50k, the math flips.
What about MPC wallets (Fireblocks, Copper, etc.)?
Excellent for institutions. Generally over-engineered (and over-priced) for individual operators below seven figures.
How often should I rotate keys?
Hot: quarterly minimum. Warm: yearly. Cold: only after suspected compromise or signer change.
Related Reading
- Crypto Trading Bot Security Best Practices
- Top 10 MEV Bot Mistakes
- Security Revolution: Desktop vs Telegram
- VPS Setup for Crypto Bots
- FRB Trust & Verification
This article is operational guidance, not security audit. Specific risks depend on your stack, jurisdiction, and threat model. Consult a security professional for high-value setups.
Step after reading
Launch FRB dashboard
Connect your wallet, pair the node client with a 6-character PIN, and assign the contract mentioned above.
Need the signed build?
Download & verify FRB
Grab the latest installer, compare SHA‑256 to Releases, then follow the Safe start checklist.
Check Releases & SHA‑256Related Articles
Further reading & tools
Discussion
No notes yet. Add the first observation, or share the link with your team on X (@MCFRB).